Privacy
Natural Language v. Regex: The Context wars
Regexes are highly effective in the perfect world of computer data, but unfortunately the real world is much more complicated.
Privacy Tech: Understanding Internet Security
There exists a vibrant ecosystem of specialized security tools. The sad truth is that it is almost impossible to reach 100% invulnerability. What can we do to get closer?
Customers Are Demanding Privacy
In the past three years there has been a massive wake-up in customer awareness about privacy. Many customers are now refactoring how they buy, taking their business elsewhere if they don’t trust a company’s data practices.
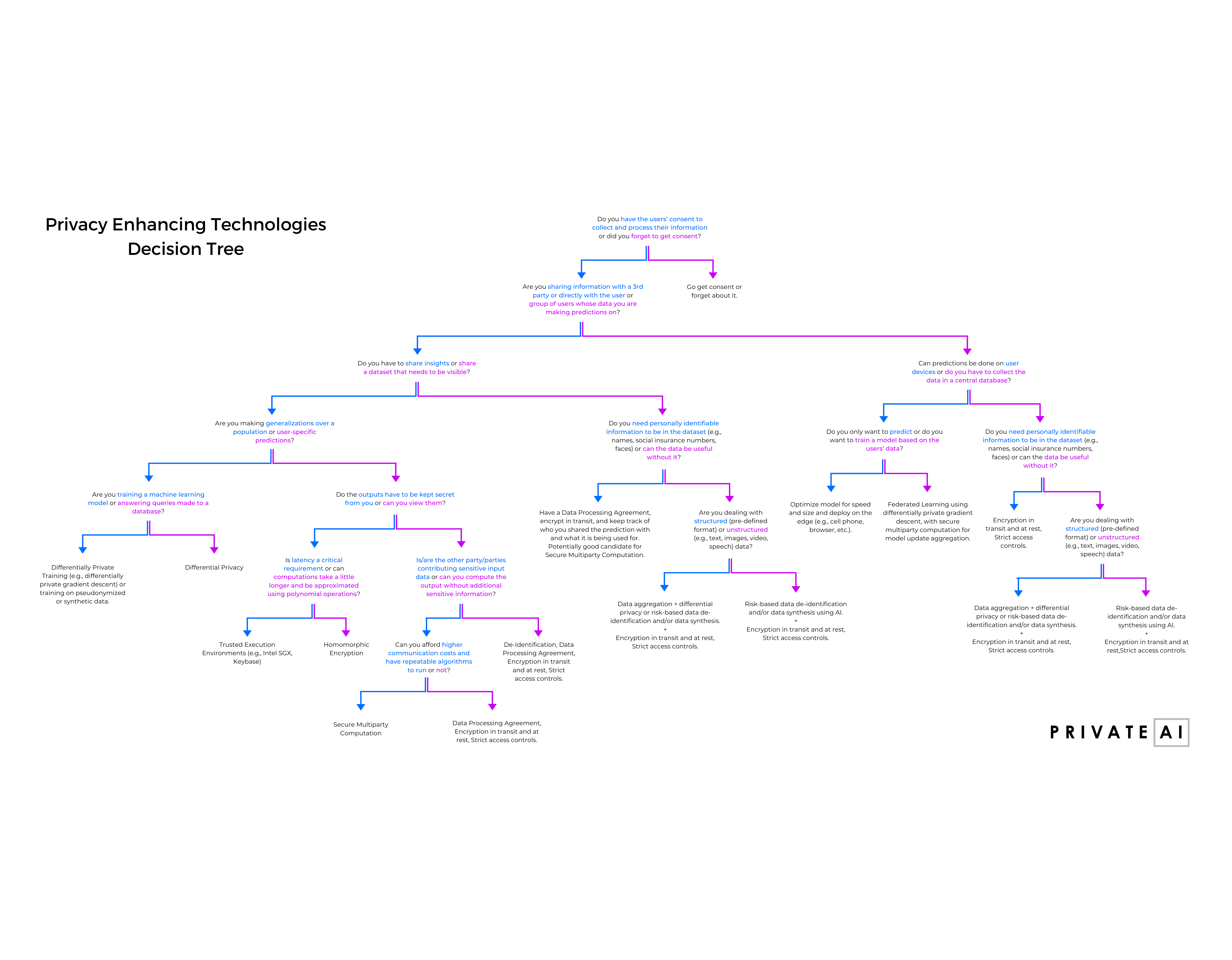
Privacy Enhancing Technologies Decision Tree
Privacy Enhancing Technologies Decision Tree:
for developers, managers, and founders looking to
integrate privacy into their software pipelines
and products.
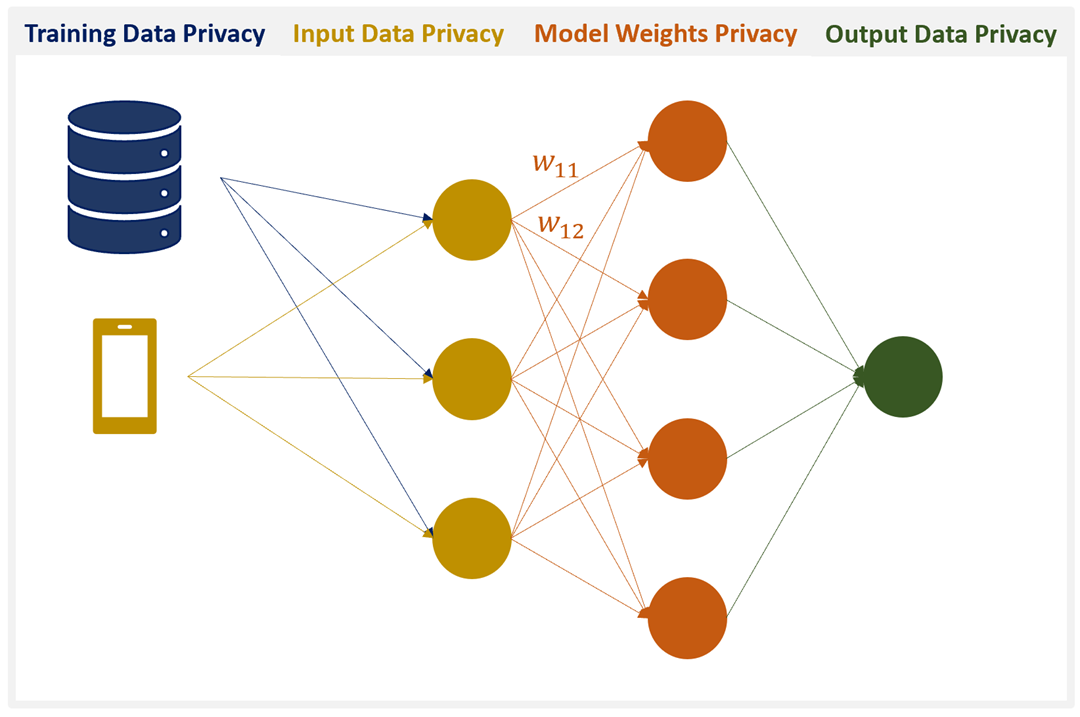
The Four Pillars of Privacy-Preserving AI
We introduce the four pillars required to achieve perfectly privacy-preserving AI and discuss various technologies that can help address each of the pillars.
Part 2: Homomorphic Encryption for Beginners
We discuss a practical application of homomorphic encryption to privacy-preserving signal processing, particularly focusing on the Fourier transform.
Part 1: Homomorphic Encryption for Beginners
We cover the basics of homomorphic encryption, followed by a brief overview of open source HE libraries and a tutorial on how to use one of those libraries (namely, PALISADE).
Why is Privacy-Preserving NLP Important?
A number of people ask us why we should bother creating NLP tools that preserve privacy. Apparently not everyone spends hours thinking about data breaches and privacy infringements.
A Brief Overview of Privacy-Preserving Technology Methods
A very brief overview of privacy-preserving technologies follows for anyone who’s interested in starting out in this area. I cover symmetric encryption, asymmetric encryption, homomorphic encryption, differential privacy, and secure multi-party computation.